Achieving ISO 27001 certification signifies excellence in information security management, demonstrating your organization’s dedication to protecting sensitive data. However, this process involves careful steps, with one of the most important being the internal audit. This crucial phase verifies that your Information Security Management System (ISMS) meets ISO 27001 standards and is strong enough to reduce risks.
Watch the Loom Video for a detailed explanation of our internal audit services, check out our Loom video, where our Principal Consultant Ali Hayat breaks down the process step-by-step and shares tips for seamless ISO 27001 compliance. Click here to watch the Loom video.

What is an ISO 27001 Internal Audit?
An ISO 27001 internal audit is a structured review of your ISMS to check its compliance with the standard’s requirements. Unlike external audits done by certification bodies, internal audits are performed by the organization itself or by a third-party auditor to find gaps, evaluate risks, and ensure readiness for certification.
The main goal of an internal audit is to ensure that your ISMS meets ISO 27001 requirements and effectively reduces risks. It also offers a chance to find areas for improvement and strengthen your organization’s security efforts. By conducting a thorough gap analysis during this stage, you help set your organization up for success in the certification process.
ISO 27001 Internal Audit Requirements: Understanding Clause 9.2
Clause 9.2 of ISO 27001:2022 establishes the specific requirements for internal audits, forming the backbone of audit governance. This section mandates that organizations establish and implement audit programs to evaluate the effectiveness of their ISMS at planned intervals.
The standard specifies several critical requirements within Clause 9.2:
Clause 9.2.1 – Audit Program Requirements: Organizations must define audit objectives, scope, frequency, and methodologies. Your audit program should establish criteria against which the ISMS will be evaluated, ensuring that all relevant information security controls are systematically reviewed over a defined period.
Clause 9.2.2 – Auditor Competence and Objectivity: This is perhaps the most critical requirement. Auditors must be objective, impartial, and free from conflict of interest. The standard explicitly prohibits auditors from evaluating areas for which they hold direct responsibility, as this compromises independence and undermines audit credibility.
To meet Clause 9.2.2, auditors should possess documented competence in ISO 27001 standards and audit methodologies. Many organizations require auditors to hold certifications such as Certified Information Systems Auditor (CISA) or ISO 27001 Lead Auditor. Reference to ISO 19011 – Guidelines for auditing management systems – provides additional guidance on selecting, evaluating, and managing auditors.
Who Can Perform an ISO 27001 Internal Audit?
Internal audits can be carried out by your organization’s own internal audit team or outsourced to a third-party auditor or an ISO 27001 consulting firm. Unlike external certification audits, you can choose the most suitable approach for your organization. However, it’s crucial to follow Clause 9.2(e) of the ISO 27001 standard, which stresses the importance of selecting an internal auditor who is objective and impartial. This means avoiding any potential conflicts of interest—specifically, the auditor should not have been involved in developing the ISMS or in operating or monitoring any of the controls under review. The reason for this requirement is simple: reviewing your own work can undermine objectivity and hinder a thorough evaluation.
Essential Auditor Qualifications
When selecting an auditor, ensure they meet the following criteria:
In-Depth ISO 27001 Knowledge: Auditors must understand the standard’s requirements, Annex A controls, and how they apply to your organization’s context.
Audit Methodology Expertise: Knowledge of audit planning, sampling techniques, evidence collection, and report writing.
Relevant Certifications: ISO 27001 Lead Auditor (IRCA or equivalent), CISA, or similar credentials demonstrate formal competence.
Industry Experience: Understanding of your sector’s specific security challenges and regulatory landscape adds significant value.
If internal expertise is limited, hiring an experienced third-party auditor or consulting firm can provide a fresh, unbiased perspective and valuable insights tailored to your organization’s unique environment.
Internal Audit vs External Certification Audit: Key Differences
Understanding the distinction between internal and external audits is crucial for effective compliance strategy. While both serve important roles, they differ significantly in purpose, scope, and outcome.
Aspect | Internal Audit | External Certification Audit |
Conducted By | Organization (internal or contracted third party) | Accredited certification body |
Primary Purpose | Identify gaps and prepare for certification | Verify compliance and issue certificate |
Focus | Detailed improvement; addresses specific findings | Overall conformance; verifies readiness |
Flexibility | High – customize scope and approach | Low – standardized audit procedures |
Internal audits serve as your organization’s opportunity to address vulnerabilities proactively before the certification audit. They foster a culture of continuous improvement and ensure that any gaps are remediated well in advance. This strategic advantage makes internal audits invaluable in the certification journey.
How to Conduct an ISO 27001 Internal Audit: Key Phases
Conducting an ISO 27001 internal audit involves a series of well-defined steps to ensure that your Information Security Management System (ISMS) is thoroughly evaluated. Below is a detailed breakdown of the process:
Phase 1: Determine the Scope of the Audit
The first step is to clearly outline the audit’s scope, specifying the systems, functions, people, and processes that will be assessed. This scope ensures the audit comprehensively covers all necessary areas to meet compliance objectives. Defining the boundaries early on helps the auditor focus on the most relevant elements of the ISMS, particularly considering your organization’s specific ISMS scope boundaries and the applicability of controls.
Phase 2: Documentation Review
Before proceeding with on-site evaluations, the internal auditor will review all key ISMS documents to verify that they align with ISO 27001 requirements. An effective ISMS requires a well-defined scope, a comprehensive Statement of Applicability (SoA), a robust Information Security Policy, a thorough risk assessment and treatment plan, and clear definitions of responsibilities. Additionally, identifying individuals responsible for implementing and operating controls, and documenting evidence of control implementation, provides valuable context for the field review.
Phase 3: Management Review and Approval
The audit plan must be reviewed and approved by senior management. Regular meetings should be scheduled to set expectations, discuss timelines, and maintain open communication. Management also plays a critical role in reviewing the internal audit findings, collaborating with the auditor to assess the organization’s readiness for an external certification audit, and ensuring that all significant issues are addressed beforehand.
Phase 4: Pre-Audit Preparation
Preparation is critical for a successful audit. This phase includes developing detailed audit checklists, identifying key personnel for interviews, scheduling on-site activities, and gathering necessary documentation. A well-prepared audit checklist aligned with ISO 27001 requirements and your organization’s context ensures comprehensive coverage and consistency.
Phase 5: Conducting the Field Review
The field review is the core of the internal audit process. During this phase, the auditor evaluates the ISMS through multiple evaluation methods, gathering evidence to support findings and determine the effectiveness of controls.
Audit Tests: Assessing controls to ensure they are effectively implemented and functioning as intended. This involves testing a sample of control activities to verify control effectiveness.
Audit Evidence Collection: Reviewing documented information and audit trails to confirm compliance and identify gaps. Evidence should support all audit conclusions.
Staff Interviews: Engaging with employees to gauge their understanding of and adherence to ISMS policies. These interviews provide crucial insight into whether controls function as designed in practice.
Observations and Documentation: Recording findings, highlighting areas of non-conformity, and identifying strengths. Clear documentation enables transparent reporting and actionable recommendations.
This comprehensive review enables the auditor to pinpoint what’s working well and what needs improvement, providing a clear roadmap for corrective actions.
ISO 27001 Internal Audit Checklist: Essential Items
A well-designed audit checklist is fundamental to conducting a thorough and consistent internal audit. The checklist should cover all ISO 27001 requirements and be tailored to your organization’s context. Below are the essential categories and items to include:
Organizational Context (Clauses 4.1-4.3): Verify that the organization understands its internal and external context, interested parties, and scope of the ISMS.
Leadership and Governance (Clauses 5-6): Confirm management commitment, information security policy, allocation of roles and responsibilities, and evidence of management review.
Planning (Clause 6): Assess risk assessment methodology, risk treatment plans, and management of information security objectives.
Support and Operation (Clauses 7-8): Check resource availability, competence assessments, awareness and training programs, and operational control implementation.
Performance Evaluation (Clause 9): Review monitoring and measurement of controls, incident management procedures, and evidence that internal audit has been appropriately planned and conducted.
Improvement (Clause 10): Evaluate management of non-conformities, corrective action effectiveness, and documented information control.
Incorporating Annex A controls into your checklist ensures that all 114 control objectives are evaluated within the scope of your ISMS. Many organizations create control-specific evaluation criteria linked to this comprehensive checklist.
Addressing Non-Conformities
Non-conformities can range from minor documentation gaps to critical security flaws. Identifying and addressing these issues promptly is essential to maintain the integrity of your ISMS. By developing comprehensive corrective action plans and monitoring their implementation, organizations can ensure continuous improvement and long-term compliance with ISO 27001 standards.
Common ISO 27001 Internal Audit Findings
Understanding typical non-conformities helps organizations proactively address vulnerabilities. Here are the most frequently encountered findings:
Documentation Gaps: Missing, incomplete, or outdated policies, procedures, or records. For example, risk assessment documentation that doesn’t clearly link to implemented controls.
Access Control Deficiencies: Inadequate user access reviews, orphaned accounts, lack of segregation of duties, or insufficient multi-factor authentication implementation.
Incident Management Issues: Incomplete incident logs, lack of timely incident classification, or insufficient root cause analysis documentation.
Training and Awareness Gaps: Insufficient security awareness training records, lack of role-specific training, or no evidence of competency assessment.
Change Management Failures: Changes implemented without proper authorization, risk assessment, or documented approvals.
Backup and Recovery Defects: Untested backup procedures, unclear recovery objectives, or lack of documented restoration testing records.
The Corrective Action Process
Addressing non-conformities requires a structured, documented approach. The standard corrective action process includes:
Classification: Categorize each finding as Major (major risk or complete absence of a control) or Minor (temporary deviation or incomplete implementation that doesn’t significantly impact security).
Root Cause Analysis: Investigate why the non-conformity occurred—whether due to lack of awareness, insufficient resources, or inadequate procedures.
Corrective Action Plan: Develop specific, measurable actions with defined timelines and responsible parties. Plans should address root causes, not just symptoms.
Implementation Monitoring: Track progress toward completion and verify that actions are implemented as planned.
Effectiveness Verification: Re-audit completed actions to confirm they have resolved the non-conformity and prevented recurrence.
Major non-conformities must be resolved before certification, while minor findings require documented action plans with appropriate timelines. Organizations should also review common mistakes during ISO 27001 implementation to avoid repeating the same errors across multiple audits.
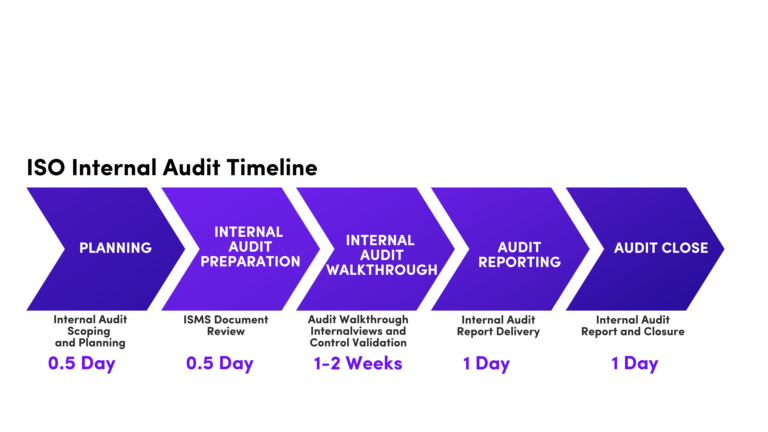
Timeline of Internal Audits
A successful ISO 27001 internal audit requires careful planning and execution. Here’s a detailed breakdown of the key phases and estimated time required for each, though actual duration depends on organization size, ISMS complexity, and control maturity.
Planning (0.5 days): Define the audit scope, objectives, and methodology. Develop an audit plan, including the schedule and resource allocation. This phase establishes the foundation for all subsequent work.
Preparation (0.5 days): Review relevant documentation, develop audit checklists, and identify key personnel to be interviewed. Preparation ensures efficiency during field activities.
Audit Execution (1-2 weeks): Conduct interviews, document reviews, and observations. Verify the implementation of controls and procedures. Identify non-conformities and opportunities for improvement. This phase is the most time-intensive and involves active on-site engagement.
Reporting (1 day): Prepare a detailed audit report, including findings, recommendations, and corrective action requirements. Review the report with management to ensure accuracy and completeness.
Closure (1 day): Finalize the audit report and distribute it to relevant stakeholders. Monitor the implementation of corrective actions. Schedule follow-up audits to verify the effectiveness of corrective actions and ensure sustainable improvement.
The audit execution timeline varies significantly based on organization size. A small organization with a well-defined scope might complete field activities in 3-5 days, while a larger enterprise with multiple business units could require 2-3 weeks. The complexity of your ISMS and the maturity of your existing controls also play significant roles in determining realistic timelines.
Benefits of a Well-Executed Internal Audit
Conducting a comprehensive internal audit provides key benefits for organizations aiming for ISO 27001 certification:
Certification Readiness: Identifying and fixing gaps before the certification audit greatly boosts the chances of passing on the first attempt and minimizes the need for re-audits.
Enhanced Security: Internal audits reinforce your ISMS by verifying control effectiveness, reducing weaknesses, and increasing your organization’s resilience to security risks.
Operational Efficiency: The process reveals inefficiencies and overlaps, helping you streamline workflows and better allocate resources for security efforts.
Stakeholder Trust: Showcasing strong, documented security practices through internal audits builds confidence with clients, partners, regulators, and other stakeholders. This often provides a competitive edge and supports business growth.
Culture of Improvement: Regular audits foster a mindset of continuous enhancement, motivating ongoing review and improvement of security measures beyond mere compliance.
Understanding Your Path to Certification with Axipro
Axipro’s internal audit services are designed to simplify the ISO 27001 compliance process. Our team of experienced auditors conducts thorough assessments, identifying gaps and providing actionable insights to strengthen your ISMS.
We tailor our approach to your organization’s unique needs, offering guidance from planning to corrective actions. With Axipro, you can streamline your internal audit process, reduce complexity, and achieve ISO 27001 certification confidently.
Conclusion
An ISO 27001 internal audit is a cornerstone of effective information security management. It ensures compliance, enhances security practices, and prepares your organization for certification success. By following a structured approach and leveraging expert support, you can make the audit process smooth and impactful.
Frequently Asked Questions
What is the purpose of an ISO 27001 internal audit?
The primary purpose is to verify that your ISMS aligns with ISO 27001 standards, identify gaps and non-conformities before external certification, ensure controls are effectively operating, and prepare the organization for successful certification audit.
Who can perform an ISO 27001 internal audit?
Internal audits can be conducted by your organization’s internal audit team or outsourced to qualified third-party auditors or consulting firms. However, auditors must be objective, impartial, and free from conflicts of interest as required by Clause 9.2.
What happens after the internal audit is complete?
After completion, the audit report is distributed to management. Non-conformities are categorized and corrective action plans are developed. Organizations then implement and monitor these corrections. Follow-up audits verify the effectiveness of corrective actions. Once major non-conformities are resolved, the organization proceeds to schedule the external certification audit.
How often are ISO 27001 internal audits required?
ISO 27001 requires audits at planned intervals, typically at least annually for certified organizations. Pre-certification organizations should conduct audits multiple times (3-6 months before certification). Focused audits can be conducted quarterly or as-needed after significant changes.
Simplify your ISO 27001 compliance journey with Axipro’s expert internal audit services.