Securing sensitive information is a critical priority in today’s data-driven world. Achieving ISO 27001 certification, an international standard for information security demonstrates a robust commitment to safeguarding data. However, before diving into the certification process, conducting an ISO 27001 gap analysis is essential to identify shortcomings in your information security management system (ISMS).
This step-by-step guide will help you understand an ISO 27001 gap analysis, its benefits, and how to execute it effectively. By following these best practices, your organization will be well-prepared for the ISO 27001 certification audit and subsequent ISO 27001 audits.

What is ISO 27001 Gap Analysis?
An ISO 27001 gap analysis is a systematic process used to evaluate an organization’s existing ISMS against the requirements outlined in ISO 27001. The goal is to identify areas where your ISMS falls short, helping you address vulnerabilities and align your processes with ISO 27001 standards.
The analysis often acts as a preliminary step before embarking on a full ISO 27001 implementation or audit, allowing organizations to uncover weaknesses without the pressure of a formal assessment.
What an ISO 27001 Gap Analysis Actually Does
An ISO 27001 gap analysis is a practical readiness check that shows how close your organization is to achieving certification and what must be addressed before audit.
Rather than implementing controls blindly, it benchmarks your current ISMS against the ISO/IEC 27001 standard published by the International Organization for Standardization (ISO), helping you focus on what auditors will actually evaluate (ISO.org).
In practice, a gap analysis delivers five core outcomes:
Certification readiness: Confirms whether required clauses and Annex A controls are defined, implemented, and supported by evidence expected during a certification audit.
Internal audit alignment: Mirrors auditor logic without the pressure of a formal internal audit, reducing surprises later.
SoA mapping: Validates that Annex A controls are correctly selected, justified, and reflected in a defensible Statement of Applicability, a common audit failure point.
Risk treatment validation: Ensures identified risks are properly assessed and linked to realistic, documented treatment plans, as required by ISO/IEC 27001 clauses 6.1.2 and 6.1.3.
Targeted remediation: Produces a prioritized remediation plan so teams address high-impact gaps first, saving time and cost.
In short, an ISO 27001 gap analysis connects the standard’s requirements to real-world implementation, creating a clear, audit-ready path instead of guesswork.
Why Conduct an ISO 27001 Gap Analysis?
Conducting an ISO 27001 gap analysis is essential for organizations that aim to strengthen their information security framework and achieve certification. Here’s a detailed explanation of why it’s critical:
- Avoid Costly Certification Failures:
Identifying non-conformities during a formal ISO 27001 certification audit can lead to delays, increased costs, and reputational risks. A gap analysis helps uncover these issues early, enabling corrective action without the pressure of a formal assessment.
- Targeted Remediation:
A gap analysis clearly identifies which areas require improvement, allowing organizations to focus their resources where they’re needed most. This targeted approach avoids unnecessary expenses and efforts in areas that are already compliant.
- Improved Risk Management:
By identifying vulnerabilities and compliance gaps, organizations can address potential security risks before they lead to breaches. Proactive risk mitigation ensures sensitive data remains protected, reducing exposure to threats.
- Streamlined Audit Preparation:
Addressing gaps in advance ensures a smoother and less stressful experience during formal ISO 27001 audits. It minimizes the likelihood of surprises during the certification process and ensures that your organization is fully prepared to demonstrate compliance.
When to Conduct a Gap Analysis (Pre- vs Post- Implementation vs Audit)
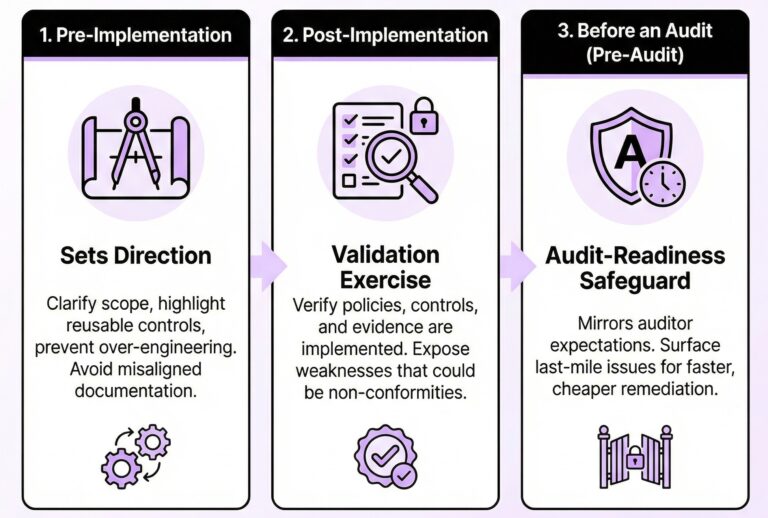
Timing matters. An ISO 27001 gap analysis delivers value at multiple stages, but the outcome changes depending on when it is performed.
Pre-implementation, a gap analysis sets direction. It clarifies scope, highlights existing controls that can be reused, and prevents over-engineering the ISMS. This is where organizations avoid building documentation and processes that do not map cleanly to ISO 27001 requirements.
Post-implementation, the gap analysis becomes a validation exercise. It checks whether policies, controls, risk treatment, and SoA mapping are not just written, but implemented and evidenced. At this stage, it exposes weaknesses that could turn into non-conformities during audit.
Before an audit, a gap analysis functions as an audit-readiness safeguard. It mirrors certification auditor expectations and surfaces last-mile issues early, when remediation is still faster, cheaper, and lower risk.
In practice, the strongest compliance programs treat gap analysis as a strategic checkpoint, not a one-time task.
Key Benefits of ISO 27001 Gap Analysis
Enhanced Security Posture:
A thorough gap analysis helps organizations identify and resolve weaknesses in their ISMS, resulting in a more robust security framework that protects against internal and external threats.
Cost-Effectiveness:
Instead of indiscriminately investing resources across all areas, a gap analysis allows organizations to allocate time, money, and effort to address specific weaknesses, optimizing overall costs.
Compliance Readiness:
A gap analysis ensures that your organization meets all ISO 27001 requirements by identifying areas of non-compliance and systematically addressing them. This sets the stage for successful certification.
Stakeholder Confidence:
Achieving ISO 27001 certification after addressing gaps demonstrates your commitment to protecting sensitive information. This builds trust with clients, partners, and regulators, enhancing your organization’s reputation.
According to a recent study, organizations with ISO 27001 certification report a 39% reduction in security incidents compared to those without certification. This highlights the importance of using tools like gap analysis to achieve compliance and enhance security.
Step-by-Step Guide to ISO 27001 Gap Analysis
Step 1: Understand the ISO 27001 Requirements
Familiarize yourself with the key elements of ISO 27001, including:
- Annex A Controls: These include 93 security controls spanning 14 domains such as access control, incident management, and supplier relationships.
- Clauses 4–10: These cover context, leadership, planning, support, operations, performance evaluation, and improvement.
Step 2: Define the Scope of the Gap Analysis
Determine which parts of your organization will be included in the analysis. This may encompass specific departments, locations, or IT systems. Clear scope definition ensures focused and relevant assessments.
Step 3: Gather Relevant Documentation
Compile existing ISMS documentation, including:
- Security policies
- Risk assessment reports
- Incident response procedures
- Training records
Step 4: Conduct the Gap Assessment
Evaluate your current ISMS against ISO 27001 requirements. Common methods include:
- Interviews with key personnel
- Reviewing processes and records
- Technical assessments of IT systems
Step 5: Analyze the Findings
Document all gaps and categorize them based on the following:
- Criticality: High-priority issues that must be addressed immediately.
- Compliance: Areas that partially meet the requirements.
Step 6: Create a Roadmap for Compliance
Develop an actionable plan to address the gaps. This should include:
- Timelines for remediation
- Resource allocation
- Assigned responsibilities
Mandatory Documents & Evidence Required for Gap Analysis
A gap analysis is only as strong as the evidence behind it. Auditors do not assess intent. They assess documentation, implementation, and proof. This is where many organizations fall short.
At minimum, a credible ISO 27001 gap analysis requires a Statement of Applicability (SoA) that clearly maps selected Annex A controls to your risk posture and justifies any exclusions. Without a defensible SoA, certification readiness cannot be reliably assessed.
Your risk assessment and Risk Treatment Plan (RTP) must show how information security risks are identified, evaluated, and treated, with clear ownership and status. These documents form the backbone of the ISMS and are directly referenced during audits.
Operational evidence matters just as much. This includes incident logs demonstrating how security events are handled, an up-to-date asset inventory showing what is protected, and access control records proving least-privilege enforcement across systems.
Third-party risk is another frequent gap. Vendor due diligence records are required to show how suppliers are assessed and monitored for security risk, especially when they process or access sensitive data.
Finally, auditors expect proof that controls operate in practice. Security training records confirm employee awareness, while audit logs provide technical evidence that systems are monitored and reviewed.
A gap analysis that reviews all of these artifacts does more than identify missing documents. It reveals whether your ISMS can withstand real audit scrutiny.
Deliverables & Outputs from a Proper Gap Analysis
A proper ISO 27001 gap analysis does not end with observations. It produces clear, usable outputs that move the organization closer to certification.
The primary deliverable is a gap analysis report that maps current practices against ISO 27001 clauses and Annex A controls, clearly distinguishing what is compliant, partially compliant, or missing. This gives leadership and technical teams a shared, factual view of readiness.
Equally important is a prioritized remediation plan. Instead of generic advice, it identifies what must be fixed first, why it matters for audit outcomes, and how remediation should be approached to reduce risk and effort.
A strong gap analysis also validates or corrects critical ISMS artifacts, including the Statement of Applicability and risk treatment decisions. By the end, organizations are not guessing what auditors will flag. They have a focused path forward, grounded in evidence and aligned with certification expectations.
ISO 27001 Gap Analysis Structure
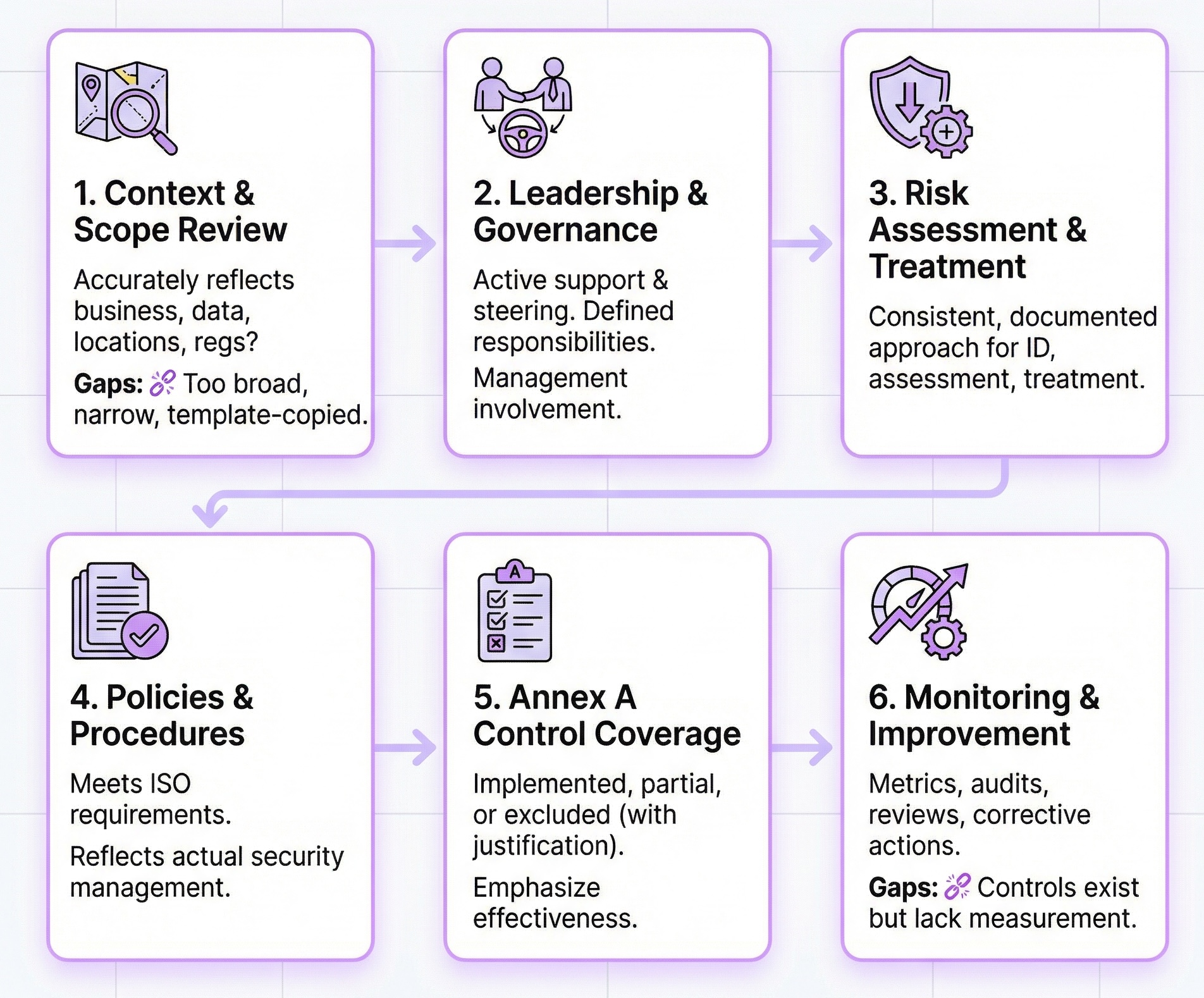
An ISO 27001 gap analysis reviews your current security posture against the ISO/IEC 27001 standard to identify what is already in place, what is missing, and what needs improvement before certification. It is a practical exercise focused on clarity and prioritisation rather than audit judgement.
The structure aligns with the ISO 27001 clauses and Annex A controls maintained by the International Organization for Standardization (ISO). A high-level overview of the standard is available here.
1. Context and Scope Review
This step checks whether the ISMS scope accurately reflects your business activities, data flows, locations, and regulatory obligations. Gaps often appear where scopes are overly broad, too narrow, or copied from templates rather than tailored to reality.
2. Leadership and Governance Alignment
The analysis reviews management involvement, ownership of information security, and defined responsibilities. ISO 27001 expects leadership to actively support and steer the ISMS, not delegate it in isolation.
3. Risk Assessment and Risk Treatment
Here, the focus is on whether risks are identified, assessed, and treated using a consistent, documented approach. The gap analysis also checks that selected controls are clearly linked to risk treatment decisions, often informed by ISO 31000 principles.
4. Policies, Procedures, and Documentation
Existing documentation is reviewed to confirm it meets ISO 27001 requirements and reflects how security is actually managed day to day. Common gaps include missing policies or documents that exist but are not followed in practice.
5. Annex A Control Coverage
This section assesses which Annex A controls are implemented, partially implemented, or excluded, and whether exclusions are clearly justified. The emphasis is on effectiveness and relevance rather than implementing every control by default.
Studies referenced by the European Union Agency for Cybersecurity (ENISA) consistently show that well-implemented controls reduce risk more effectively than broad but shallow coverage.
6. Monitoring, Measurement, and Internal Audit
The final review examines how security performance is monitored through metrics, internal audits, management reviews, and corrective actions. Gaps here often indicate that controls exist but are not actively measured or improved.
Together, these sections form a clear, structured view of readiness, enabling a focused remediation plan and a smoother path to ISO 27001 certification.
Common Challenges in ISO 27001 Gap Analysis
Conducting an ISO 27001 gap analysis can be daunting due to several challenges organizations often face. Understanding these hurdles and how to address them is key to a successful outcome.
- Lack of Expertise
ISO 27001 is a comprehensive standard that demands specialized knowledge. Organizations without skilled personnel may inadvertently overlook critical gaps, leaving vulnerabilities unaddressed. This can lead to compliance failures during certification audits.
Solution: To ensure an in-depth and accurate analysis, engage internal team members with ISO 27001 training or hire external consultants with proven expertise.
- Insufficient Resources
Many organizations need more time, budget, or staff for the gap analysis. This can result in incomplete assessments or rushed evaluations, increasing the risk of missed issues.
Solution: Allocate sufficient resources by prioritizing the analysis in your security strategy. Break the process into manageable phases and consider external support to optimize efficiency.
- Resistance to Change
Employees may refrain from adopting new policies, processes, or technologies introduced as part of ISO 27001 compliance. This resistance can slow down implementation efforts and compromise the effectiveness of the gap analysis findings.
Solution: Foster a culture of security awareness through clear communication, training programs, and involving employees in the compliance journey.
- Complex IT Environments
Modern organizations often operate in intricate IT ecosystems, including on-premises systems, cloud services, and hybrid setups. Assessing compliance across such environments can be challenging due to varying security configurations and integration issues.
Solution: Use advanced tools and frameworks to assess IT systems comprehensively. To streamline the process, partner with experienced consultants familiar with modern IT environments.
Partnering with an Experienced Consultant
Collaborating with ISO 27001 consultants can help organizations overcome these challenges effectively. Consultants bring specialized knowledge, tools, and experience to guide organizations through the complexities of gap analysis, ensuring a smoother path to compliance.
How to Prepare for the ISO 27001 Certification Audit
Once you’ve addressed the gaps identified in your analysis, it’s time to prepare for the ISO 27001 certification audit. A well-prepared organization can ensure a seamless certification process and minimize delays.
1. Internal Audit
Conduct an internal audit to evaluate your compliance with ISO 27001 requirements. This will help identify residual non-conformities and validate the effectiveness of corrective actions taken during the gap analysis.
2. Management Review
Involve leadership in reviewing the ISMS. This step ensures top-level commitment, aligns security goals with organizational objectives, and highlights areas needing further attention before the certification audit.
3. Staff Training
Employees play a crucial role in maintaining compliance. Train them on their responsibilities within the ISMS, emphasizing adherence to new policies, procedures, and controls.
4. Documentation
ISO 27001 heavily relies on documentation. Ensure all required policies, processes, risk assessments, and corrective action records are up-to-date, accurate, and easily accessible for auditors.
The Growing Importance of ISO 27001 Certification
ISO Survey data shows a 20% annual growth in ISO 27001 certifications worldwide, reflecting its increasing relevance in today’s security-conscious business environment. Achieving certification protects your organization’s data and builds trust with clients and partners, offering a competitive edge in the market.
Statistics and Trends in ISO 27001 Compliance
- Global Adoption: Over 58,000 organizations worldwide are ISO 27001 certified, a testament to its widespread recognition.
- Breach Prevention: Companies with ISO 27001 certification are 50% less likely to experience major data breaches.
Cost Savings: Effective compliance reduces the average cost of a data breach, which stands at $4.45 million, according to IBM’s 2023 Cost of a Data Breach Report.
Conclusion
An ISO 27001 gap analysis is foundational for organizations seeking to strengthen their information security systems. By identifying and addressing deficiencies early, businesses can ensure smoother ISO 27001 certification audits and ongoing ISO 27001 audits.
Adopting a systematic approach enhances security and builds trust with stakeholders, giving your organization a competitive edge.
At Axipro, we specialize in efficiently helping businesses achieve ISO 27001 compliance. Contact us today to begin your journey towards robust information security.
FAQs
- What is an ISO 27001 gap analysis, and why is it important?
An ISO 27001 gap analysis evaluates your current information security management system (ISMS) against the requirements of ISO 27001. It helps identify areas for improvement to achieve compliance and strengthen your security posture.
- Who should conduct an ISO 27001 gap analysis?
Internal security professionals, an internal audit team, or external consultants specializing in ISO 27001 compliance can conduct a gap analysis. Organizations often choose external experts to gain an unbiased perspective.
- How long does an ISO 27001 gap analysis take?
The duration depends on your organization’s size and complexity and the scope of the analysis. It can take anywhere from a few days to several weeks.
- What documents are needed for an ISO 27001 gap analysis?
You’ll need existing ISMS policies, risk assessment reports, incident management procedures, access control policies, and other relevant security documentation.