Most organisations that fail their first ISO 27001 certification audit don’t fail because their security is lacking. They fail because they lack a systemic approach to their IT systems. ISO 27001:2022 is not a technology exercise. It is a governance framework, and getting certified requires your entire organisation to demonstrate that it manages information security systematically, continuously, and with documented intent.
This guide provides a practical, phase-by-phase roadmap to ISO 27001 implementation, covering everything from initial scoping to certification audit preparation. Whether you are building an ISMS from scratch or modernizing a legacy system, the structure below reflects how implementation actually works in practice.
The ISO 27001 Implementation Roadmap at a Glance
An ISO 27001 implementation roadmap is a structured project plan that takes an organization from its current security posture to certified compliance with ISO/IEC 27001:2022. The roadmap defines phases, deliverables, roles, and timelines, giving your team a clear line of sight from day one through to the certification audit.
The standard itself has two components. Clauses 4 through 10 define the mandatory management system requirements: context, leadership, planning, support, operations, performance evaluation, and improvement. Annex A provides a reference catalogue of 93 security controls, organised into four themes: organisational (37 controls), people (8 controls), physical (14 controls), and technological (34 controls). A well-structured roadmap addresses both components in a logical sequence, with risk driving every decision.
Prerequisites and Planning Before You Start
Define the Scope of Your ISMS
Scope definition is the single most consequential decision in the entire implementation. The scope should reflect the business units, locations, processes, and information assets that are most critical to your organization and most relevant to your customers and stakeholders.
A well-defined scope document should identify the boundaries of the ISMS, the interfaces and dependencies with external parties, and any intentional exclusions, with justification for each. Auditors scrutinize scope boundaries carefully. Any exclusion that appears to cherry-pick convenient systems will attract challenge.
Form Your ISO 27001 Implementation Team
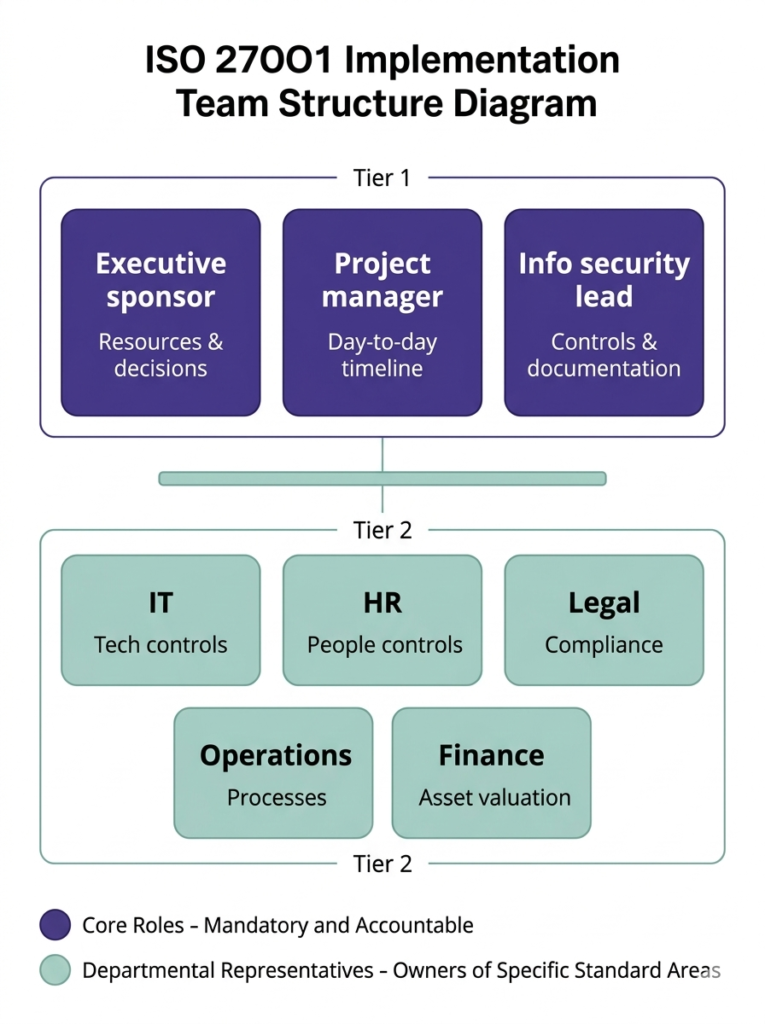
Three roles are non-negotiable: an executive sponsor with authority to allocate resources and enforce decisions; a project manager who owns the day-to-day implementation timeline; and an information security lead who understands both the technical controls and the documentation requirements. Larger organisations may also need departmental representatives from IT, HR, legal, and operations.
The most common implementation failure mode is assigning ISO 27001 entirely to the IT team. The standard requires evidence that security is embedded across the organisation. HR owns the people controls. Legal owns the contractual and regulatory requirements. Finance owns the asset valuation. If those functions are not engaged early, you will discover gaps at the worst possible time. If your organisation lacks in-house expertise, working with an experienced ISO 27001 consultant can bridge that gap efficiently.
ISO 27001 Implementation Roadmap: Phase-by-Phase Breakdown
Phase 1 (4 to 7 weeks): Foundation and Planning Phase
The first 30 to 45 days establish the governance foundation. Key deliverables include a documented ISMS scope; an approved information security policy signed by top management; a defined organisational context covering internal and external issues, interested parties, and legal requirements; and a completed gap assessment that maps your current state against the standard’s requirements.
From this list, the gap assessment is the most important document. It identifies which controls are already in place, which need to be built from scratch, and which exist informally but require documentation. Our gap analysis services are designed specifically for this phase, helping organisations cut through the ambiguity and get a clear remediation picture fast.
Phase 2 (2 to 4 weeks): Implementation Phase
The second 15 to 30 days focus on risk and documentation. Your team completes the formal risk assessment, identifies and values assets, maps threats and vulnerabilities, and determines risk levels against your defined risk appetite. From this, you produce a Risk Treatment Plan that specifies which risks will be mitigated, accepted, transferred, or avoided, and which Annex A controls address each risk.
The Statement of Applicability (SoA) is produced during this phase. It documents all 93 Annex A controls, the justification for including or excluding each one, and the current implementation status. The SoA is typically the first document an auditor requests. It connects your risk assessment to your control selection and demonstrates that your ISMS is risk-driven rather than checklist-driven.
Phase 3 (1 to 3 weeks): Audit and Approval
The final phase focuses on executing the controls, training staff, and preparing for audit. Technical controls from the risk treatment plan are deployed. Operational procedures are finalised and approved. Security awareness training is delivered to all staff. An ISO 27001 internal audit is conducted to identify nonconformities before the certification body arrives. A management review is completed to demonstrate leadership engagement.
This 90-day timeline is achievable for small to mid-size organisations with existing security foundations and dedicated implementation resources. Larger organisations, or those starting from a low security baseline, should plan for up to 6 months. Rushing the process to meet an arbitrary deadline is the leading cause of audit failures and certification theatre, a situation where documented controls exist only on paper and fall apart under auditor questioning. For a detailed breakdown of where implementations go wrong, see our guide on common pitfalls in ISO 27001.
12-Week Detailed Implementation Timeline
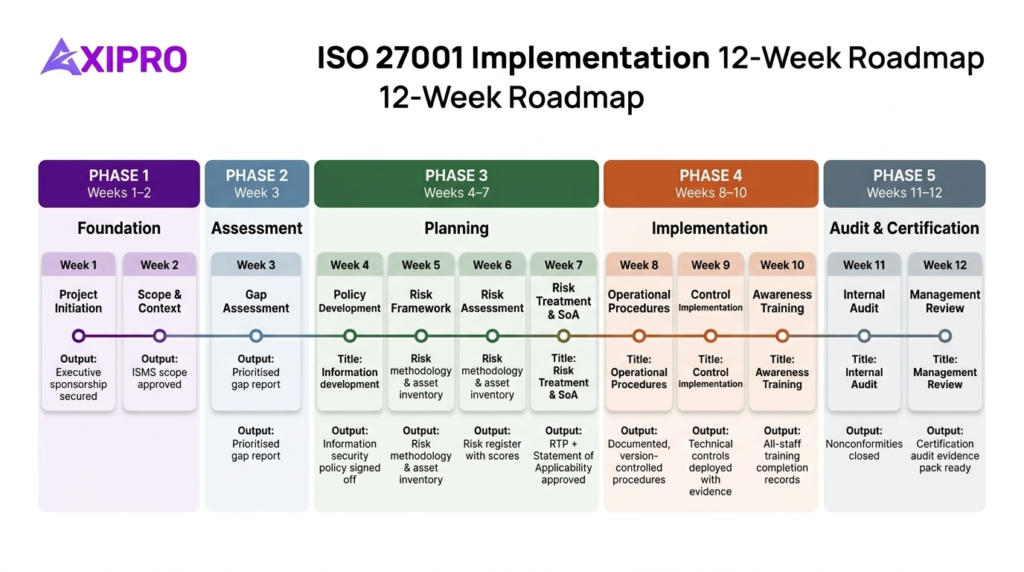
Week 1: Project Initiation
Secure executive sponsorship in writing. Establish the project team and define roles. Brief key stakeholders on the standard’s requirements and business case. Set up project governance, including a steering committee and regular status reporting.
Week 2: Define ISMS Scope and Context
Document the organisational context using Clause 4 requirements. Identify interested parties and their requirements. Define and document the ISMS scope boundary. Obtain approval from top management.
Week 3: Gap Assessment
Assess current security controls against ISO 27001 requirements and all 93 Annex A controls. A thorough ISO 27001 gap analysis produces a gap report that quantifies the remediation work required, prioritises gaps by risk impact and implementation effort, and forms the foundation of a credible project plan and budget.
Week 4: Policy Development and Leadership Alignment
Draft the overarching information security policy. Develop supporting topic-specific policies covering areas such as access control, acceptable use, incident management, and supplier relationships. Obtain formal approval from top management.
Week 5: Risk Assessment Framework
Define the risk assessment methodology, including criteria for likelihood, impact, and risk acceptance thresholds. Create the asset inventory. Establish the risk register structure and tooling. Agree the risk appetite with the executive sponsor.
Week 6: Conduct Risk Assessment
Identify and assess information security risks across all assets and processes within scope. Assign risk owners. Evaluate each risk against the defined criteria. Produce the initial risk register with risk scores and preliminary treatment decisions.
Week 7: Risk Treatment Plan and Statement of Applicability
Develop the Risk Treatment Plan with control selections, owners, timelines, and residual risk levels. Produce the Statement of Applicability, documenting justifications for all 93 Annex A controls. Obtain formal approval from management.
Week 8: Develop Operational Procedures
Document operational procedures for the selected controls. These are the how-to instructions that evidence the controls are actually being operated, not just defined. Procedures should be concise, practical, and version-controlled.
Week 9: Control Implementation
Deploy technical controls from the risk treatment plan. This typically includes access controls, network security configurations, logging and monitoring, backup and recovery systems, and physical security measures. Capture evidence of implementation as you go. For organisations with significant technical exposure, this is also the right point to schedule vulnerability assessment and penetration testing to validate that controls are functioning as intended.
Week 10: Employee Security Awareness and Training
Deliver security awareness training to all staff within scope. Cover key policies, reporting obligations, phishing and social engineering awareness, and incident escalation procedures. Record completion. Auditors routinely test staff awareness during the Stage 2 audit — this is not a box-tick exercise.
Week 11: Internal Audit
Conduct the internal audit against all applicable clauses and Annex A controls. The internal auditor must be independent of the processes being audited. Document findings, classify nonconformities and observations, and issue corrective actions. Verify that corrective actions are implemented before the certification audit.
Week 12: Management Review and Certification Preparation
Conduct the management review, covering ISMS performance, audit results, risk status, and improvement opportunities. Produce formal management review minutes. Assemble the certification audit evidence pack. Confirm Stage 1 and Stage 2 audit logistics with the certification body.
Key Stages of the ISO 27001 Certification Process
ISO 27001 Readiness Assessment
Before engaging a certification body, organisations typically conduct an internal readiness assessment to evaluate whether the ISMS is mature enough for external audit. This is distinct from the gap assessment conducted at the start of implementation. The readiness assessment asks whether documented controls are operating effectively, whether evidence is available and current, and whether staff can demonstrate awareness of their security responsibilities.
Gap Assessment
The formal ISO 27001 gap analysis maps your current security posture against the standard’s requirements. It identifies missing documentation, absent controls, and areas where informal practices need to be formalised. A well-executed gap assessment produces a prioritised remediation list that forms the foundation of the implementation plan.
Stage 1 Audit
The Stage 1 audit is a documentation review. The auditor evaluates whether your ISMS is designed correctly: whether the scope is defined, whether the information security policy is in place, whether the risk assessment has been completed, and whether the Statement of Applicability is present and coherent. Stage 1 typically lasts one to two days. Any major nonconformities identified at Stage 1 must be resolved before Stage 2 can proceed.
Stage 2 Audit
The Stage 2 audit is the certification audit. The auditor conducts an on-site or remote assessment of whether the controls documented in your ISMS are actually operating effectively. Auditors interview staff, review evidence records, inspect systems, and test whether the processes described in your documentation match what is happening in practice. A Stage 2 audit typically takes three to seven days depending on organisation size.
Experienced auditors ask questions that reveal whether controls are understood or just documented. They ask staff: what would happen if a server went down, how they would report a phishing email, who is responsible for approving access to sensitive data. Your answers must be consistent with your documented procedures. Zero incidents reported is a red flag, not a sign of excellence.
Surveillance Audit
ISO 27001 certificates are valid for three years. Annual surveillance audits — typically shorter than the initial certification audit — verify that the ISMS continues to operate effectively and that improvements are being made. Surveillance audits focus on areas where nonconformities were previously identified, as well as any significant changes to the organisation, its risk environment, or its technology landscape.
Recertification
At the end of the three-year cycle, a full recertification audit reassesses the entire ISMS. This resembles the original Stage 2 audit in scope and depth. Organisations that have maintained their ISMS diligently through annual surveillance cycles typically find recertification straightforward. Those that have allowed the ISMS to drift often face significant remediation work before they are ready to re-engage the certification body.
Core Components of ISO 27001 Implementation- Checklist
Build Your Information Security Management System (ISMS)
The ISMS is the governance framework above all individual controls, defining how your organisation identifies risks, operates controls, and improves. It requires active leadership and clear accountability, not just a folder of policies.
Create and Publish ISMS Policies, Procedures, and Documentation
Policies set direction, procedures describe execution, and records prove compliance. All three are mandatory and all three are assessed at audit.
Conduct Risk Assessment and Risk Treatment
Every control decision flows from the risk assessment, identifying assets, mapping threats, estimating likelihood and impact, and documenting treatment decisions. Aim for 40 to 80 well-scoped risks rather than hundreds of near-identical entries.
Prepare the Statement of Applicability (SoA)
The SoA lists all 93 Annex A controls and justifies every inclusion and exclusion. You do not need to implement every control, but unjustified exclusions are a leading cause of Stage 1 failures.
Implement Access Control and Authentication Processes
Access must be granted on a need-to-know basis, reviewed regularly, and revoked promptly when staff leave. MFA is required as a minimum for all remote and privileged access.
Protect Against Network and Web-Based Threats
Network segmentation, intrusion detection, vulnerability management, and the 2022 additions of web filtering (A.8.23) and data leakage prevention (A.8.12) are baseline expectations, auditors want to see them operating with documented evidence.
Ensure Data Backup and Recovery
Backups must be tested and proven restorable. Auditors ask for evidence of recovery tests, not just confirmation that backups are being taken.
Implement Physical Security Measures
Entry controls, visitor management, clean desk policies, and secure media disposal are all in scope. These controls are routinely underestimated in planning, budget time for them early.
Monitor and Review Your ISMS
Define what you measure, how often, and what triggers action. Monitoring outputs must feed into management reviews, which produce documented improvement decisions.
Continuously Improve Your ISMS
Nonconformities from audits, incidents, or reviews must be root-cause analysed, resolved, and verified closed. This cycle is what separates a functioning ISMS from one that exists only on paper.
Mandatory Documents Required for ISO 27001 Implementatio
ISO 27001:2022 mandates a specific set of documented information. Auditors request these as a baseline during Stage 1:
- ISMS Scope (Clause 4.3) — defines the boundaries and applicability of the management system
- Information Security Policy (Clause 5.2) — top management’s formal commitment to information security
- Risk Assessment Process (Clause 6.1.2) — your methodology for identifying, analysing, and evaluating risks
- Risk Treatment Plan (Clause 6.1.3) — documented decisions on how each identified risk will be treated
- Statement of Applicability (Clause 6.1.3d) — the definitive reference for all 93 Annex A control decisions
- Information Security Objectives (Clause 6.2) — measurable targets linked to the policy and risk assessment
- Evidence of Competence (Clause 7.2) — training and qualification records for ISMS-related roles
- Operational Planning Results (Clause 8.1) — evidence that security operations are carried out as planned
- Risk Assessment Results (Clause 8.2) — the documented output of the risk assessment process
- Internal Audit Programme and Results (Clause 9.2) — confirmation that internal audits have been planned and conducted
- Management Review Records (Clause 9.3) — minutes and decisions from management reviews
- Nonconformity and Corrective Action Records (Clause 10.1) — documentation of identified nonconformities and their resolution
How to Accelerate Your ISO 27001 Implementation
Common Delays to Avoid
Scope creep. Expanding scope mid-project forces rework across the risk assessment, SoA, and documentation set. Define boundaries precisely at the start and hold them.
Weak executive engagement. Implementations stall at policy approvals and resource decisions when sponsors delegate and disengage. The sponsor should attend steering meetings and have weekly visibility during active phases.
Late-stage documentation. Deferring documentation until after controls are implemented produces thin, retrospective evidence. Write documentation in parallel with implementation, not after.
Accelerators That Speed Up the Process
Templates. ISO 27001-aligned policy and procedure templates can compress the documentation phase by several weeks. Adapt them to your context rather than treating them as off-the-shelf compliance.
GRC tools. Purpose-built platforms provide structure for risk registers, the SoA, and audit evidence management — replacing spreadsheets that become unmanageable at scale. Our compliance tools comparison covers the leading platforms in depth.
External consultants. Their value is pattern recognition: they know what auditors scrutinise, which documentation gaps attract nonconformities, and what a credible risk assessment looks like. For organisations without in-house expertise, consultant engagement typically pays for itself in avoided rework. Our Compliance Accelerator Program offers a structured, supported path to certification through software automation with a free 30-day trial.
Pro Tip: Timeline Gaps
Run Stage 1 before you are fully ready for Stage 2. Most certification bodies allow a gap of several weeks between stages, use Stage 1 findings as a final remediation checkpoint to sharpen your evidence pack before the certification assessment.